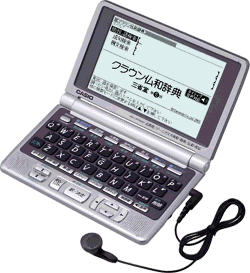
I had some time to hack around the USB connection of my casio dictionary, and I have reached a “duh” point: the protocol used by the dictionary is OBEX run over USB. This is somehow surprising as OBEX is typically used over IRDA or Bluetooth not USB. What I though were commands are basically object names that are read and set. Now the content of the initial response packet makes perfect sense:
| Bytes | Meaning |
|---|---|
A0 |
Success |
00 07 |
Packet length: 7 bytes |
11 |
OBEX version: 1.1 |
00 |
Flags: None |
08 00 |
Max packet size: 2K |
The bad news is that I should scrap most of my code, the good news is that now I could use the OBEX code in Mac OS X, and implement an OBEX Session on top of USB, and use the library calls to handle the put and get operations.
It comes from the IrDA but it is a long time it has been used over other physical layers of which USB.
And I think I already read that the Nokia mobile phones use Obex over Usb to download/upload personnal data from/to the mobile flash memory.
You can also have a look on OpenObex implementing both a client and a server.
But I really don’t like how it is coded (abstraction layers not well defined to handle the transport layer and the obex application layers themsleves).
Bascially you have operations (connect/disconnect, get/put, etc…) which coudl be customized with headers (body/end of body, description, length, etc…).
When you have the spec in the hand, it is really easy to implement a basic support of the protocol.
I was planning on using the class offered by OS X which implements all the header handling. I just need to implement the read-write logic to the USB pipes. The difficult part is figuring out what the get/put operations control what functionality on the device.
You have to snif the obex frames in the case of the japanese dico to check which headers are used during the get (0x02/0x82 if final bit set) /put (0x03/0x83 if final bit set) operations.
I think you should fine at least the “Name” header (0x01) and maybe also the object “Length” header (OxC3).
You also may find a “SetPath” operation (0x85) in the frames if the dico transfer is done in 2 steps (selecting the path then storing the object).
After such a reverse engineering, you’ll would be able to know which headers are required to be able to upload/download the files.
However, if there is an authentication challenge (0x4D and 0x4E headers for the request and the response), except if it is a magic number, it will be quite hard to achieve your goal…
Hope it Helps
I have some traces, the get/put are all final.
I have seen get operations with the following names: _Model, _List, _Cap
_List returns the two storages of the device: _INTERNAL_00, _SD_00
_Capacity returns the storage capacity (after a select into it).
Select commands are issued against those two names.
Put commands are used to upload files, but they are preceded by two puts and a get.
• Put Name (_Unlock) Length (1) End of Body(00)
• Put Name (_Cname) Length (8) End of Body(30 30 31 00 54 58 54 00)
• Get Name (_CryptKey) Header (x71) “DUMMY_USER” \0 “001”\0 “001” 43 53 65 6E 99 50 08 → Length(12) End of Body(44 55 7D 7D 8A 5F 98 A6 AA C0 00 00)
The actual put has Name, Length and End of Body headers, end of body contains the file content.
• Finally there is a GET for _Lock with Length(1) and EOB(00)
There is clearly some key exchange going on in the _Cname / _CryptKey operations.
And what occurs if you try to put an other files than the Japanese dico?
Is the file then refused by the device?
The 0x71 does not correspond to any specified header in the official obex spec.
If you want to continue discussing by email to prevent polluting the comment section of your article, feel free to contact me. Don’t know if I am skilled enough, but if I can, it will be with pleasure…
Thanks, I’ll send you an e-mail!
Hello,
I bought an EW-A6400 and am very much interested in your research.
port 2 addr 2: high speed, self powered, config 1, CESG502(0x6101), CESG502(0x07cf), rev 1.00
I started writing a small test app with the Python bindings for libusb-0.1.12, but
now I need more information about the protocol and/or USB trace logs to proceed.
For various reasons, usbsnoop is quite unusable on my XP test box, a netbook.
I have a few traces, but could use more, contact me by e-mail, and I’ll send you them if you want…
Thias,
I picked up a second hand Ex-Word XD-SW4800 (DataPlus 3) on eBay to help me with my studies of Japanese (Did two semesters at Uni, so basically beginner).
Here is the output of mine in USB Probe.app
Full Speed device @ 4 (0x0B200000): ……………………………………… Composite device: “CESG502”
Device Descriptor
Descriptor Version Number: 0x0200
Device Class: 0 (Composite)
Device Subclass: 0
Device Protocol: 0
Device MaxPacketSize: 64
Device VendorID/ProductID: 0x07CF/0x6101 (Casio Computer Co., Ltd.)
Device Version Number: 0x0100
Number of Configurations: 1
Manufacturer String: 1 “CASIO”
Product String: 2 “CESG502”
Serial Number String: 0 (none)
Configuration Descriptor
Length (and contents): 39
Raw Descriptor (hex) 0000: 09 02 00 27 01 01 00 C0 32 09 04 00 00 03 FF 00
Raw Descriptor (hex) 0010: FF 00 07 05 82 02 40 00 00 07 05 01 02 40 00 00
Raw Descriptor (hex) 0020: 07 05 83 03 08 00 02
Number of Interfaces: 1
Configuration Value: 1
Attributes: 0xC0 (self-powered)
MaxPower: 100 ma
Interface #0 – Vendor-specific
Alternate Setting 0
Number of Endpoints 3
Interface Class: 255 (Vendor-specific)
Interface Subclass; 0 (Vendor-specific)
Interface Protocol: 255
Endpoint 0x82 – Bulk Input
Address: 0x82 (IN)
Attributes: 0x02 (Bulk no synchronization data endpoint)
Max Packet Size: 64
Polling Interval: 0 ms
Endpoint 0x01 – Bulk Output
Address: 0x01 (OUT)
Attributes: 0x02 (Bulk no synchronization data endpoint)
Max Packet Size: 64
Polling Interval: 0 ms
Endpoint 0x83 – Interrupt Input
Address: 0x83 (IN)
Attributes: 0x03 (Interrupt no synchronization data endpoint)
Max Packet Size: 8
Polling Interval: 2 ms
I suspect I know where the encryption is used on the dictionary.
When one installs contents onto the dictionary (In my case I bought the CD-ROM with Jack Halpern’s Kanji Learner’s Dictionary for Casio), at least onto the SD card, the resulting data gets encrypted. I can’t yet verify if the encryption uses some internal ID of a dictionary (so one can’t move an SD card from one dictionary to another) or if it uses something else, like the username on the dictionary. Technically since Casio sells SD cards with contents, it’s possible that the data on the SD card should be accessible by any Ex-Word, but I only have one to test with.
I know the the username of the account used in Casio ライブラリ application gets preserved on the SD card together with the contents, and the contents are encrypted, but I haven’t tried creating two different usernames under Casio ライブラリ, copying the same data to card, and comparing the results.
I suspect that the second place encryption is used in the factory reset steps for the Ex-Word.
Since my dictionary is second hand, it came with a username set (`KOSUKE` in my case). This is what gets displayed on the screen when you press power-off button. Of course I’d rather change that, but username gets preserved through the reset.
Based on my research, in order to do a full reset of the dictionary, one has to use the Casio ライブラリ application, and select the appropriate option from the pull-down menu. A challenge gets presented by the software, and Casio expects you to enter the challenge into a form on their web site (Registration required, and in order to register one needs a serial number of the dictionary), and get a response key. According to Casio web page and my sloppy understanding of Japanese, this response key is used to decrypt something on the dictionary that authorizes the erasure of that part of configuration.
A couple of questions for you:
1) Do you know if there is a way to programatically obtain the serial number of the dictionary? Maybe something you see in your USB traces? Serial number of the back of my dictionary faded into illegibility, and I need the serial number to register with Casio and obtain the factory reset code. Grrr.
2) Do you need any USB traces of contents (Well, KALD, the only thing I have) being installed onto Ex-Word, or erased from it? I can install a USB sniffer on a laptop with Windows XP, and generate those for you. What USB tracer do you use, snoopy or usb snoop? It’s been a few years since I tinkered with USB, but I guess I’ll start on this again.
Ideally, I’d love a command line or GUI application that would allow one to connect to the dictionary, upload and download contents from it and from the SD card in it, and (And I know that this is a bit of a farfetched thing) maybe even do the factory reset thing (or at least initiate the crypto exchange, generate the key needed for submission to Casio, and send a user supplied reply back to the dictionary). Sadly I am not really all that good a coder – little code that I write is generally high level and has to do with text parsing or formatting on Unix systems, not with things like OBEX. Is there any way I can help?
Any other way I can help?
I managed to compile Brian Johnson’s e libexword (http://github.com/brijohn/libexword/ ) under Linux last night, and play around with my XD-SW4800
Here are my findings so far:
root@jolicloud:~/exword/brijohn-libexword-53294a8/src# ./exword -?
Usage: lt-exword [OPTION…]
–sd access external sd card
–internal access internal memory (default)
–list list files on device
–send send file to device
–delete delete file from device
–model get device model
–capacity get device capacity
–scan scan system for device ids
–file=STRING file name to transfer/delete
–device=STRING usb device (eg 0c7f:6101)
–debug=INT debug level (0..5)
Help options:
-?, –help Show this help message
–usage Display brief usage message
root@jolicloud:~/exword/brijohn-libexword-53294a8/src# ./exword –scan
Devices:
0: 07CF:6101 CASIO CESG502
root@jolicloud:~/exword/brijohn-libexword-53294a8/src# ./exword –device=07cf:6101 –model
Model: gy131,ON,0101
OK, Success
root@jolicloud:~/exword/brijohn-libexword-53294a8/src#
Need to reconnect USB on the EX-Word at this point.
This would be the first thing I am going to try fixing in libexword – extending this application with a –disconnect command, and only sending disconnect USB command on demand, not after each command.
root@jolicloud:~/exword/brijohn-libexword-53294a8/src# ./exword –device=07cf:6101 –capacity
Internal Capacity: 52428800 / 42395500
OK, Success
root@jolicloud:~/exword/brijohn-libexword-53294a8/src#
50 megs internally, about 10 of which are used by the installation of Jack Halpern’s Kanji Learners Dictionary (KALD).
Need to reconnect USB on the EX-Word at this point.
root@jolicloud:~/exword/brijohn-libexword-53294a8/src# ./exword –device=07cf:6101 –list
fav.inf
authinfo.inf
drvvewer.inf
admini.inf
jpush.wrk
jlpush.wrk
user.inf
line3.inf
siorivi.inf
OK, Success
root@jolicloud:~/exword/brijohn-libexword-53294a8/src#
Again, need to reconnect USB at this point.
I am guessing that is likely “Ogura Hyakunin Isshu”/100 poems by 100 poets. Just a guess.
is the subdirectory created by uploading of KALD onto the device (I know this because if I put KALD onto an SD card, and access the SD card in the card reader, this is the directory that is created), so
The rest of the directories are likely the other dictionaries. There is no way to list the contents of a subdirectory using the current revision of libexword AFAICT.
So this would be the second area that I’d be interested in improving – I’d like to attempt to extend libexword to read the contents of the subdirectories, and to present more information on the files (If available), such as sizes, modification dates, etc.
If there would be a way to back up dictionaries, it could be very interesting too.
With no SD card inserted into the device:
root@jolicloud:~/exword/brijohn-libexword-53294a8/src# ./exword –device=07cf:6101 –sd –list
Internal server error
root@jolicloud:~/exword/brijohn-libexword-53294a8/src#
I will see about fixing this, making it more graceful. It could be as simple as changing the error message, and leaving everything as is.
Regarding the Casio Textloader – I experimented with the Casio TextLoader that Casio releases for the two models of the dictionary on Russian market (On Russian market there are EX-Word EW-R2000V and EW-R100, with only the former supporting officially supported by Casio Textloader. In fact I am not convinced that EW-R100 even has an USB port). XD-SW4800 is not supported – Under Windows the application says that the device is unsupported, and the dictionary itself says that the protocol is incorrect.
Same story with German version of Casio TextLoader (But my German is alot weaker then my English, so I might misinterpret the error message somewhat. Bottom line is it doesn’t work).
Any way, that’s the story so far.
Thanks a lot for the information!
Hello guys, any progress since last update?
I have XD-SF7700 with Russian dictionary onboard, but there is much better dictionary available in web for free, and I wonder if there is way to recompile it to be used with Casio…
Thias, Evgeny
Check out libexword.
https://github.com/brijohn/libexword
Check out the development branch.
Compile it, install it, run it against your dictionary.
If your dictionary is not Japanese, connect using “connect library “. “connect library cn” works against EV-SP2900 Chinese/English dictionary, support for all other dictionaries (German, French, Russian, etc) is theoretical (For technically inclined, Casio uses different OBEX version in the OBEX connect string to initiate connection).
Run “model” command, and e-mail the output, together with information about the model of your dictionary to Brian.
You can reauthenticate against your dictionary, basically do the same thing that Casio Ex-Word Library software does. You can back up user-installed dictionaries.
Eugeny, you can’t really make your own dictionaries for the device yet. While the dictionaries that Casio sells in the Japanese market are not that hard to copy to PC from the device, and then decrypt, the format for them is not fully understood yet.
Send me an e-mail, if you’re interested in working on these.
cypher321 at yandex.
Thanks cypher321, I’ll a have a try as soon as I’ll have some time.
There is a Chinese vedio maybe it will help http://www.youtube.com/watch?v=HP-KFBLyRRk This video is made by some unscrupulous merchant which maybe have some connection with China manufactory company who wants to profiteer by selling ROM flashed dictionary. It flash the XD-A7300 model to E-A300 model.
What important is does anyone know how to enter the Test Mode?
The guy is telling there that you need a special card to update the firmware. It’s called 刷机卡
Here is the method to enter the CASIO dictionary TEST MENU
Power off dictionary
Hold the go-back key (for newer modules it is near the four navigation keys older modules it is on the left), the page up key and
the power key for maybe 5 seconds until it beeps and the screen light
on and popup a window shows the Model and the BIOS Ver
Release the three keys and press the right navigation key two times
then press enter key then it will beep two times and enter the hidden
TEST MENU
But how to hack the password of the service menu of the manual check
I confirm the trick to get to the test Menu works on my casio dictionary. Thanks!
Now I got two files to flash the CASIO E-A300 dictionary from a dealer.
http://www.mediafire.com/?amo3x2dygzsxupx
http://www.mediafire.com/?l6rz0s8me7912sa
Originally there
are three files but I only got two from him as the largerest one is
more than 1GB . He only send me the two small ones. I think these
files can give us great hit on hacking the dictionary. They are designed to be
used by put in to a SD card and select OS update in the Test Menu. But
I never tried them as one file is missing.
If the dictionary is a newer module like E-A300 (released on 2010 in
China) or E-B300 (released on 2011 in China) there is a password when
you want to enter the MANUAL CHECK > SERVICE MENU. If it is an older
module like E-SF300 (released on 2009 in China) there is no password
when you want to enter the SERVICE MENU. The SERVICE MENU has tools
that can backup the system file to the SD card. But now no one knows
what the password is. Does anyone have any ideas about how to hacking the
password?
@indaejeon
I’ve looked at your files. UPDADN5.BIN is “ROR UPDATE v7.2” (Note the the Chinese dealer in the infamous ROM flashing video has “ROR UPDATE v8.3”. It seems that the ROR updates (the flashing applications that get executed from the menu), are, at the very least, generation of dictionary specific.
ROR UPDATE v7.2 deals with CASIO PVOS 500, however a quick look at the backup of my XD-A6800 (DataPlus 5 device, internal model id CY110) tells me that DP5 devices with color screen run CASIO PVOS 600.
Further analysis shows that:
DP3 devices, like XD-SW4800 or XD-SW9400 are CASIO PVOS 400 devices
DP4 devices, like XD-GF10000, XD-SP9500, or Chinese EV-SP2900 (hardware identical to Japanese XD-SP9500) are CASIO PVOS 500 devices.
DP5 devices, like XD-A4800 or XD-A6800 are CASIO PVOS 600 devices.
While I don’t have an E-A300 handy, since it has color screen, and flashes over into a Japanese XD-A7300 (or any devices from the same generation, it seems), it is highly likely that it runs CASIO PVOS 600.
In other words, highly likely that these files are not for flashing E-A300, but for flashing older black and white DP4 dictionaries.
Now, DP5 generation had two releases in 2010. A4800/A6800/A8500, etc were all released in the beginning of the year. They, AFAIK, do not require a password to get into service menu, but need a password to restore from ROM backup onto the device. I don’t have a SW-Bxxxx (2011 models) dictionary or SW-Axx50 dictionary (second half of 2010), with which I can experiment, and thus I don’t know if the backup menu got locked out or not.
The 1 GB file that you refer to, is likely the ROM backup of the device, perhaps slightly different from the one that you can generate by running backup from service menu (since the backup file generated from that menu also includes a copy of the user installable files on the 50 meg partition).
Update: I copied these two files into a root directory of an MicroSD card formatted from the service menu of a dictionary. Then if I put the card into XD-SP9500 (DP4 device) or EV-SP2900, and select “OS UPDATE”, “UPDATE FROM FLASH CARD”, device scans till “Module 5”, and then I am greeted with the following screen:
*** ROR UPDATE v7.2 ( Src: LY865 ) ***
NAND 1 UPDATE: ** FILE NOT FOUND **
NAND 2 UPDATE: ** NO DEVICE **
NAND 3 UPDATE: ** NO DEVICE **
FIRST FORMAT:
MTP UPDATE:
NG (in huge letters)
== PUSH YAKU-KEY to RESET! ==
If you press the Yaku key, device indeed resets.
So basically, yeah, the files you were given, they work. Just that they are for a different generation of a device then you thought.
Some more comments about TEST MENU….
Of marginal interest, but the backup you can make of the device memory (Not the ROM backup, but the one done through “TEST MENU” -> “MANUAL CHECK” -> “SERVICE MENU” -> “BACKUP”) is pretty much a DOS FAT16 filesystem, with a 512 byte header identifying the model of the dictionary at the beginning.
So a quick dd if=BACKUP.BIN of=BACKUP.img bs=512 skip=1 later you can have a more or less mountable image of the internal flash.
FAT16 implementation they use has some quirks, however, so when looking through these images, occasionally I end up with corrupt directory/file listings
Another option is the “FLASH UTILITIES” -> “USERAREA COPY (DRV0 -> SD)” that just does a file by file copy of the same data to flash, instead of it being a block by block image.
Lastly, if your dictionary supports setting owner name on the welcome and farewell screens (A feature available in some Casio Ex-Word devices designed for school use, like XD-A4800 or XD-SW4800), and you forgot the 4 digit password that you assigned to it (or, in my case, bought a used dictionary on eBay, that had “KASUKE” pre-set, and, of course, no password), the […] -> “SERVICE MENU” -> “DELETE PASSWORD” function is for you. It serves no purpose in devices that don’t have the user name option in the menu (You would set this in the “regular” Options Menu, is the one that is accessible by pressing shift Enter, and generally device that doesn’t have a username set, yet supports the functionality, will ask you after every reset if you want to set it).
I finally got some files taht can be used for OS update. Anyone interested in reverse engineering or hacking the device may have a try.
http://www.mediafire.com/?82x359ztt2uww
How to get Libexword working: a short manual for Ubuntu users
1. Setting libexword up:
git clone https://github.com/brijohn/libexword.git
Installation:
. / autogen.sh
. / configure
make
make install
You may need to install libraries called libreadline-dev libusb and by
apt-get install libreadline-dev libusb-1.0 libusb-dev
2. If you run exword and it returns an error (missing library), then you will need to copy files from / libexword/scr/.lib to /usr/lib and keep a list of files copied.
cp -v libex* /usr/lib > install.log
3. Connecting the dictionary:
Select the PC-link in the menu.
Hit enter on the keyboard dictionary, follow the instructions on the screen.
Start exword as root.
Enter the connect [mode] [language]
For example connect library cn
I found a “taisyukan Grand Chinese-Japanese Dictionary” ,which is originally inside A7300 or B7300 (not the Shogakukan C-J Dictionary), been hacked and now can be installed into every machine.
I have tried EXWORD.EXE but failed to access the mem area (“hontai”).
The taisyukan Grand C-J doesn’t have a CD version, so it must be exported from B7300 or A7300 other than from a CD.
I just wonder is there a way to access the mem area?I mean the dictionaries installed originally.
Please, upload it somewhere!
I don’t have the files but I’ve seen a clip online of a B10000 with Grand C-J installed inside.
Analyzing data from @indaejeon I found out that DATAOUT dumps contains some ECC (error correction codes) after each 512-bytes sector. So data extracted directly from DATAOUT is not reliable and could contain sporadic bit-errors, at least if you don’t know ECC correction algorithm. Without algorithm one could use two DATAOUT dumps from different devices to recover erroneous bits (it should be DIFFERENT devices of the same model, because flash memory usually fails at the same locations). Interestingly enough that vendor-originated dumps do not contains error-correction, so ECC probably is added while uploading data to device. I’ve tried to compare files extracted from my XD-A7700 DATAOUT dumps with those from vendor-originated CY177D0B.BIN, and some files are actually different, but errors are pretty rare – only a few bits. Thus to extract data from DATAOUT we need more dumps. Or vendor dumps. Or we need to reverse-engineer ECC algorithm.
It’s a pity dumps from most advanced model B10000 are not complete, it missing NACE2 part, so even not-corrected data could not be extracted.
hey, i’m looking for XD-SP7300 update files (a quite old casio version i guess), i only got those of XD-SP7700 for the learning of Russian (interesting, but not too useful for me at this moment), so has anyone got any clue on this?
I’m desperate. XD-SP7300 OR XD-SP7500, either is cool. Thanks!
Could you upload the files you have somewhere?
It would be nice to analyze them.
Someone has managed to decypher the broken encoding! :)
http://item.taobao.com/item.htm?spm=1103JNuy.3-1RmIz.h-MRAgk&id=6883043769&
I will try to get it
It’s very sad that there has been very little progress in creating custom dictionaries for CASIO dics. If anyone is interested in cooperation in the field, you could mail me: ankeqiang ( AT ) gmail.com
Hey all!
If you’re interested in libexword, creating custom dictionaries for CASIO or anything related to the topic, we could chat at #libexword channel on Freenode, North America. The chat room was created by brijohn, the author of Libexword.
You’re welcome to share ideas and files!
All right, I’m on IRC but I don’t see anyone.
@ indaejeon Would you like to share your files with us again? Or
@ zuzian Would you like to share with us your A7700 dataout?
Sorry for the documents moved away from public folder, I don’t want to have a lawsuit or something with casio.
Does anyone know of any dictonaries that have been emulated? It seems to me that there would be a market for such an emulator. I have seen various emulators such as the TI calc emulator and seems like there should be a dictionary emulator somewhere out there.
Hi,
if I press the the keys for entering the menu on my EW-G7000E only appears “Password delete…” . After a few seconds follows “complete!”.
What does this mean?
Hello there? is someone here? i found this place trying to find some information above Casio’s ex-word dictionaries data loading capabilities… So hello =)
hi guys i am trying to flash my ex-word memory and try to install windows ce or any othe system to use it as pocket pc or gameboy like game any ideas ??
alumina, that seems like a perfect waste of a great electronic dictionary. Tons of portable machines come with Windows installed, and you can buy new mini devices today that have it. For Gamboy emulation, you’re betting off installing an emulator on a device with buttons like a DS or PSP, and standalone devices are also sold. (this project exists, but not sure which dictionaries it works for, if it does at all: https://github.com/brijohn/gnuboy-ex)
Even if it were possible to install Windows, if you follow the discussions here, Ex-Word devices have not been sufficiently understood and hacked. The purpose of doing so would be to load our own software or dictionaries onto the device rather than replacing the firmware.
I wish these devices ever get cracked. Would be nice to change which dict the hardware shortcut buttons open. Installing other dictionaries would be amazing, such as JMDict or EPWINGs. Could be cool to add other methods of typing kanji such as by multiple radical lookup (rather than the current main radical + stroke count). Some Exword models have a screen at the bottom, which would be really cool to configure to show J-E definitions when using the jump function. Etc., etc.
For what it’s worth, modern dictionaries no longer seem to work with libexword out of the box. There seems to be still OBEX transfers under the hood, but the connect fails in all modes. Maybe if I get bored later I’ll fire up the protocol sniffer and see what’s going on, but I’m usually busy with other projects.